ABOUT_
CIPHER (Cybersecurity Intelligence, Protection, and Holistic Enterprise Resilience) aims to tackle and provide demonstrable solutions for security and information assurance in critical sectors. It develops a collaborative, standardized, and available-as-a-service testing facility for security strategies and enablers qualification.
Core methodology:
The project envisions associating a fabric of solution providers, essential service operators, and external auditors to build adapted, efficient, and compliant security measures. CIPHER adopts a demanding evaluation strategy by involving three internal use-case providers contributing to programmatic requirements identification and internal validation.
Experimentation laboratory
Developing and integrating a laboratory serving pre-emptive security capability contributing to increased preparedness.
Holistic resilience
Protecting critical infrastructures (Energy, Transport, Telecoms) against sophisticated attack campaigns.
Regulator compliance
Fostering compliance with the EU’s cybersecurity strategy (NIS2, DORA) and fostering technological sovereignty.
OBJECTIVES_
TECHNICAL OBJECTIVES_
TO1.
Collaborative Experimentation Platform
TO2.
Dynamic Risk & Threat Assessment
TO3.
Automated Pentesting (TO3)
TO4.
Security Countermeasures & Response
TO5.
Trustworthy Information Sharing (TO5)
TO5.
Advisory & Compliance Services
IMPACT_
CIPHER enhances the resilience and security of critical infrastructures across the European Union by offering crucial support in three key areas:

Preparedness support services
- The platform serves as a testing and training environment for essential service providers to evaluate cybersecurity governance.
- It facilitates realistic attack simulations via Cyber-range capabilities and supports cybersecurity exercises across different sectors (e.g., transport, telecommunications).

Threat & risk assessment services
- Deploys a dynamic risk assessment framework integrating threat intelligence feeds and predictive risk assessment (UEBA).
- It supports automated pentesting activities to provide continuous evaluation of attack surfaces.

Risk monitoring services
- Provides continuous risk monitoring through attack surface monitoring and vulnerability tracking.
- It facilitates ongoing assessment of security controls and enables cross-border collaboration and joint exercises for collective cybersecurity posture.
WORKPLAN_
The CIPHER project implementation comprises eight Work Packages (WP).
WORK PACKAGES_

Project Management and Consortium Coordination
This work package ensures effective project management, overall coordination with the Granting Authority, data management, and ethics compliance throughout the project lifecycle.
Lead: EVIDEN
Cyber-Risk & Threat Assessment
WP2 establishes the framework for cyber-risk and threat assessment by analyzing external threat intelligence sources to blueprint security risks.
Lead: CERCA-i2CAT

Increased Preparedness though Risk Monitoring and Countermeasure Evaluation
This work package implements real-time risk monitoring agents and develops a security response manager to enhance preparedness.
Lead: ICCS

Pentesting and Simulation Environment
WP4 develops the flexible deployment framework, automated penetration testing tools, and the Cyber-range facility for safe experimentation.
Lead: EVIDEN

Security Advisory Services
This work package provides AI-driven security recommendations and tools for regulatory compliance checking (e.g., NIS2, DORA), along with secure data management.
Lead: K3Y

Integrated CIPHER Platform & Internal Pilot Demonstrators Preparation
WP6 integrates the complete CIPHER platform architecture and coordinates the implementation of the three internal pilot demonstrators.
Lead: EXZ

Open Calls Management
This Work Package manages the entire lifecycle of the Open Calls and the distribution of Financial Support to Third Parties (FSTP) to foster innovation.
Lead: F6S

Project Management and Consortium Coordination
WP8 defines and executes the communication, dissemination, and exploitation strategies to maximize community engagement and project impact.
Lead: INTERACTIVE4D
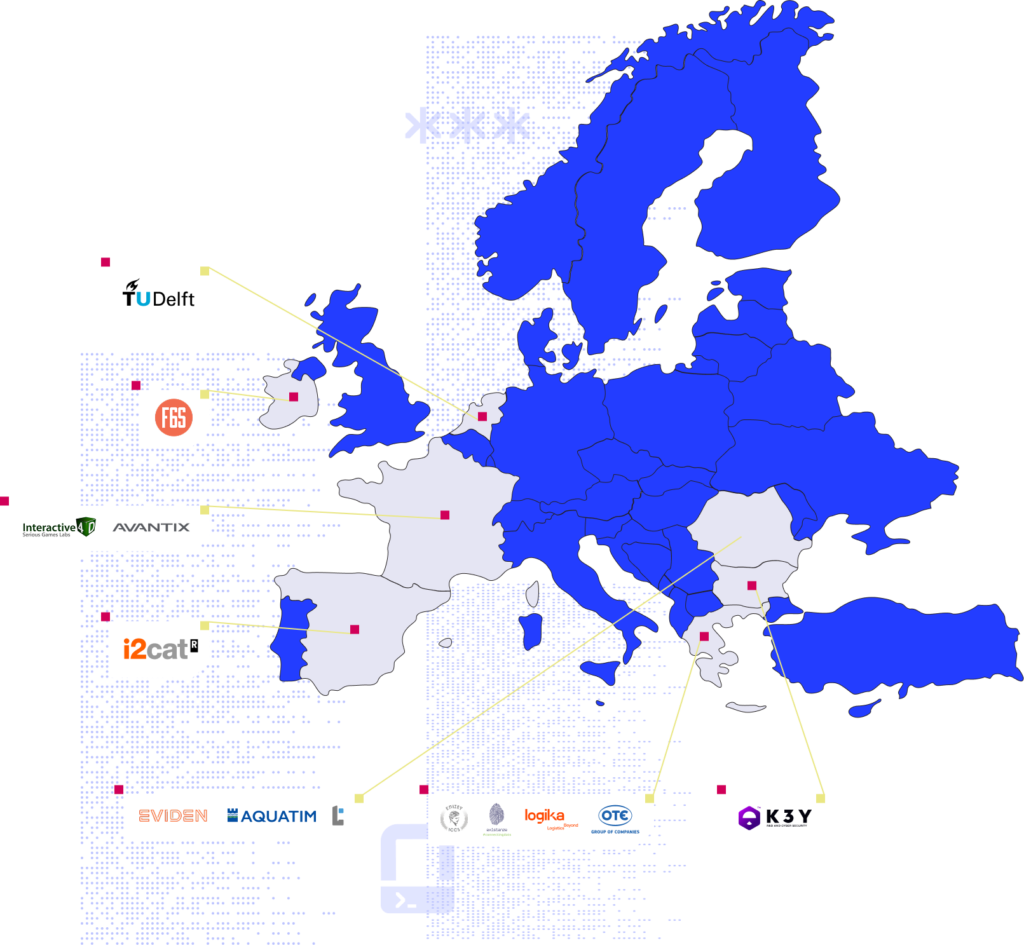
01 EVIDEN Technologies SRL (EVIDEN)
Eviden is an Atos Group business, a global leader in digital transformation. Eviden Technologies Romania operates as a key hub for R&D, specializing in advanced computing, security, and digital platforms.
They offer top-tier services in software development, cybersecurity, Big Data, and High Performance Computing (HPC). Their ambition is to coherently address cybersecurity through a holistic approach (people, processes, technology), focusing on cyber incident detection, impact assessment, and automated response.
Role: As the Project Coordinator, Eviden holds the helm of the consortium (WP1) while simultaneously driving the technical development of the pentesting and simulation environments (WP4). They leverage their industrial-grade expertise to implement Zero Trust architectures and Security Operations capabilities.

02 FUNDACIO PRIVADA I2CAT, INTERNET I INNOVACIO DIGITAL A CATALUNYA (i2CAT)
The i2CAT Foundation is a non-profit research and innovation centre based in Barcelona that promotes mission-driven R&D activities. They are committed to designing the future digital society by leveraging knowledge in 5G/6G, IoT, immersive technologies, and cybersecurity. Their Cybersecurity research group specializes in Cyber-threat management, user-centric security, and risk assessment, integrating technologies like Artificial Intelligence and Robot Process Automation.
Role: i2CAT orchestrates the Cyber-Risk & Threat Assessment efforts as the Leader WP2. Their primary mandate involves designing the privacy toolkit based on User Entity Behavior Analytics (UEBA) and analyzing diverse threat intelligence sources to feed the platform.
03 EREVNITIKO PANEPISTIMIAKO INSTITOUTO SYSTIMATON EPIKOINONION KAI YPOLOGISTON (ICCS)
Linked to the National Technical University of Athens (NTUA), ICCS is a non-profit research institute that performs top-quality research and development. The Information Management Unit (IMU) participating in CIPHER focuses on cloud and edge computing, cybersecurity, access control, and distributed data management. ICCS has vast experience in coordinating European R&D projects and is a member of key associations like IDSA.
Role: ICCS spearheads the initiatives for Increased Preparedness through Risk Monitoring as the Leader of WP3. They are in charge of deploying federated monitoring agents and establishing blockchain-based mechanisms for continuous authentication.

04 AQUATIM SA (AQUATIM)
Aquatim S.A. is the leading regional water and wastewater operator in Timiș County, Romania. With over 130 years of experience, the company provides essential services to more than 500,000 residents, operating an extensive infrastructure network. Aquatim stands out for its ambitious digitalization strategy, implementing advanced solutions such as SCADA systems and smart consumption monitoring.
Role: Aquatim serves as the Pilot Provider for the Water Utility sector (WP6). They provide a critical live environment to test and validate CIPHER’s detection capabilities within a converged IT/OT infrastructure, ensuring the solution meets real-world utility needs.
05 EXISTANZ - CONNECTING DOTS IPIRESIES PLIROFORIKIS IDIOTIKI KEFALAIOUCHIKI ETAIRIA (EXZ)
Existanze – Connecting Dots is a leading ICT solutions provider based in Athens, Greece, with over 20 years of experience delivering tailored software development and systems integration. Security and authorization are at the core of their work, specializing in identity and access management (IAM), data protection, and secure cloud architectures.
Role: Connecting Dots holds a strategic dual mandate as Leader of WP6 (Integrated Platform) and Leader of WP8 (Dissemination & Exploitation). They are the technical architects behind the platform integration while ensuring the project’s results are effectively communicated to the market.

06LOGIKA APOTHIKEFSEIS EMPOREVMATON MONOPROSOPI ETAIREIA PERIORISMENIS EYTHINIS (LOGIKA)
LOGIKA is a premier logistics provider, offering end-to-end transportation and warehousing solutions on a global scale. Specializing in multimodal transport, the company handles air, sea, and road freight. Committed to technological innovation, LOGIKA places cybersecurity at the core of its operations to ensure secure digital transactions and supply chain integrity.
Role: LOGIKA acts as the Pilot Provider for the Logistics sector (WP6). They bring CIPHER into the field to stress-test cybersecurity preparedness in cross-border scenarios, covering complex operations like warehousing and real-time fleet tracking.

07K3Y (K3Y)
K3Y Ltd is a dynamic SME from Sofia, Bulgaria, specialising in cybersecurity and Research and Development (R&D). K3Y offers a diverse range of AI-driven cybersecurity solutions, emphasizing intrusion and anomaly detection, threat intelligence, and intelligent honeypots. They develop research products such as K3CyberRadar and K3DecoyNet.
Role: K3Y manages the Security Advisory Services as the Leader of WP5. They are tasked with delivering AI-driven security recommendations and developing the Regulatory Compliance Checker to ensure adherence to standards like NIS2 and DORA.

08TEMERON SRL (TEMERON SRL)
Based in Timișoara, Romania, TEMERON is an SME that specializes in cybersecurity, software development, IoT, and AI-driven solutions. As a trusted technology integrator, they deliver high-quality, tailored solutions to small businesses and multinational corporations alike, ranging from advanced threat detection to AI-powered IoT solutions.
Role: Functioning as a Technology Provider, TEMERON integrates specialized tools into the Risk Management framework (WP2). Their contribution focuses on developing the Risk Management Toolbox and visualization modules for threat assessment.
09TECHNISCHE UNIVERSITEIT DELFT (TU DELFT)
Delft University of Technology (TU Delft) stands as the oldest and largest technical university in the Netherlands. The Faculty of Technology, Policy, and Management brings world-class expertise in context-aware access control and usage control for data management, as well as the trustworthiness, non-repudiation, and traceability of analytics.
Role: TU Delft acts as a Research & Technology Partner (WP3). They provide academic oversight and technical solutions for Continuous Federated Risk Monitoring, utilizing Distributed Ledger Technology (DLT) to ensure the trustworthiness of the platform.

10ORGANISMOS TILEPIKOINONION TIS ELLADOS OTE AE (OTE)
The Hellenic Telecommunications Organisation S.A. (OTE), part of Deutsche Telekom Group, is the leading telecom provider in Greece. OTE operates advanced Network Management and Security Operations Centers (NMC & SOC), with strong expertise in threat detection, incident response, and IT security.
Role: OTE operates as the Pilot Provider for the Telecommunications sector (WP6). They demonstrate the platform’s scalability by showcasing how CIPHER streamlines alert management and automates threat detection in a high-volume carrier environment.

11F6S NETWORK IRELAND LIMITED (F6S)
F6S is the leading global network and platform for application management and growth in the commercial, corporate, government, and university innovation spaces. With over 1.5 million tech startups and 2.7 million entrepreneurs, F6S delivers billions in funding to startups annually. F6S tracks emerging trends across industries with insights based on internal expertise and its strong network of project partners, corporates, universities, and startups.
Role: F6S is the designated Leader of WP7 (Open Calls), managing the distribution of cascade funding to third parties and all the communication. Additionally, they contribute their community building expertise to support the dissemination efforts (WP8).

12AVANTIX
Avantix, an Atos business, specialises in developing advanced solutions for critical systems across air, land, and maritime domains. With deep technology expertise in Electronic Intelligence (ELINT) and Communication Intelligence (COMINT), they bring years of experience in wireless protocol security to the consortium.
Role: In CIPHER project, Avantix leads the development of vulnerability assessment agents and automated penetration testing. Their primary focus is on automating the testing of wireless protocols to identify and secure potential entry points in critical infrastructures.
13INTERACTIVE4D
Interactive4D is a French studio specialising in the design and development of serious games, gamified e-learning tools, and interactive simulations. They have extensive experience in creating educational tools for cybersecurity awareness (such as “Beware!” and “Cyber Crime”), aiming to modify behaviors and improve preparedness through immersive learning experiences.
Role: Interactive4D leads the project’s Dissemination, Exploitation, and Community Engagement work package. They are responsible for the project’s communication strategy, the development of the official Guidebook, and ensuring that CIPHER’s research results are successfully transitioned into sustainable, market-ready applications